The cryptocurrency revolution promised to return financial control to individuals, eliminating the need for traditional banks and intermediaries. Yet as millions of people have discovered, this promise comes with a daunting responsibility: the need to secure their own digital assets. Unlike traditional banking, where forgotten passwords can be reset and lost cards can be replaced, cryptocurrency operates under the unforgiving principle that lost keys mean lost funds forever.
The situation remains dire for those using non-custodial wallets, where losing both the password and seed phrase typically results in permanent inaccessibility to funds. Ledger analysts note that between 2.3 million and 3.7 million Bitcoin (BTC) is estimated to be lost globally, representing billions of dollars in permanently inaccessible wealth. These staggering figures underscore a fundamental challenge that has persisted since Bitcoin's earliest days: how can ordinary people safely manage their own financial sovereignty?
The answer lies in an evolving landscape of wallet technologies, each representing a different approach to balancing security, usability, and control. From the traditional seed phrase system that has dominated cryptocurrency for over a decade, to sophisticated multi-signature arrangements, to cutting-edge multi-party computation protocols, we are witnessing a transformation in how digital assets are secured and accessed.
This evolution reflects more than just technological advancement. It represents a fundamental shift in how we think about trust, control, and risk in the digital age. As we stand at the threshold of mainstream cryptocurrency adoption, understanding these technologies becomes crucial not just for crypto enthusiasts, but for anyone preparing for a future where digital assets play a central role in the global economy.
The Foundation: Understanding Seed Phrases
To appreciate the innovations in wallet technology, we must first understand the system that has served as cryptocurrency's backbone since its inception: the seed phrase. Think of a seed phrase as the master key to a vast digital safe. A seed phrase, also known as a recovery phrase, acts as a master key to access your cryptocurrency holdings, offering a safety net in case of device loss, theft, or malfunction.
When you create a cryptocurrency wallet, you're actually generating a cryptographic key pair consisting of a public key (which serves as your wallet address) and a private key (which proves ownership and allows spending). The seed phrase is essentially a human-readable representation of your private key, typically consisting of 12 or 24 words chosen from a standardized dictionary. These words might look random – something like "abandon ability able about above absent absorb abstract absurd abuse access accident" – but they contain the mathematical foundation for all your cryptocurrency addresses and private keys.
The beauty of this system lies in its simplicity and universality. Even if you lose access to your wallet (such as a lost hardware wallet or damaged phone), you can regain access to your wallet using a recovery phrase. This same seed phrase can restore your wallet on any compatible device, anywhere in the world, at any time. It's a form of financial portability that was impossible in the traditional banking system.
However, this elegance comes with profound responsibility. The seed phrase represents complete and irrevocable control over your funds. Unlike a bank account where you can prove your identity to regain access, cryptocurrency operates on the principle of mathematical proof rather than trusted identity. If someone gains access to your seed phrase, they can drain your wallet completely, and there's no customer service department to call, no fraud protection to rely on, and no way to reverse the transaction.
The practical implications of this responsibility have proven challenging for many users. We found that the majority of our participants harbored significant misconceptions about seed phrases that could expose them to significant security risks — e.g., only 43% could correctly identify an image of a seed phrase, many believed they could reset their seed phrase if they lost them. These misconceptions point to a deeper problem: the gap between the sophistication required to manage seed phrases safely and the technical knowledge of average users.
Consider the storage challenge alone. The most secure approach requires writing your seed phrase on paper and storing it in multiple secure, offline locations. Some individuals who use cryptocurrencies keep their seed phrases in places such as a bank vault or a secure deposit box to safeguard them from theft and potential risks, like fire or water damage. Yet this creates its own problems: how do you balance redundancy against exposure? How do you ensure your family can access your funds if something happens to you? How do you protect against natural disasters while maintaining accessibility?
The digital storage alternative seems attractive but introduces different risks. Storing your recovery phrase on a computer or in the cloud increases the risk of it being compromised by hackers or malware. The cryptocurrency world is littered with stories of users who lost everything because they took a screenshot of their seed phrase, saved it in their password manager, or stored it in their email drafts.
Even more insidious are the psychological vulnerabilities that seed phrase management creates. The scam assumes that our nefarious passerby will want to appropriate all or at least part of the cryptocurrency. Sophisticated scammers exploit users' lack of understanding about seed phrases, creating elaborate scenarios where victims voluntarily share their recovery phrases in the mistaken belief they're helping someone or claiming a reward.
The human factor represents perhaps the greatest weakness in the seed phrase system. People make mistakes, they forget things, they trust the wrong individuals, and they make decisions under stress that they later regret. Although 22% of participants shared seed phrases for recovery purposes, many participants acknowledged the importance of planning for account recovery but did not take corresponding actions.
These challenges have led to what security experts call the "usability-security tradeoff." The more secure you make seed phrase storage, the more difficult it becomes to use. The more convenient you make it, the more vulnerable it becomes to theft or loss. This fundamental tension has driven the development of alternative approaches that maintain security while reducing the burden on individual users.
Yet despite these challenges, seed phrases remain the foundation of cryptocurrency self-custody. They embody the core principle of cryptocurrency: that individuals, not institutions, should control their own money. Every innovation in wallet technology must grapple with this fundamental concept while trying to make it more accessible, secure, and practical for widespread adoption.
The Evolution to Multi-Signature Security
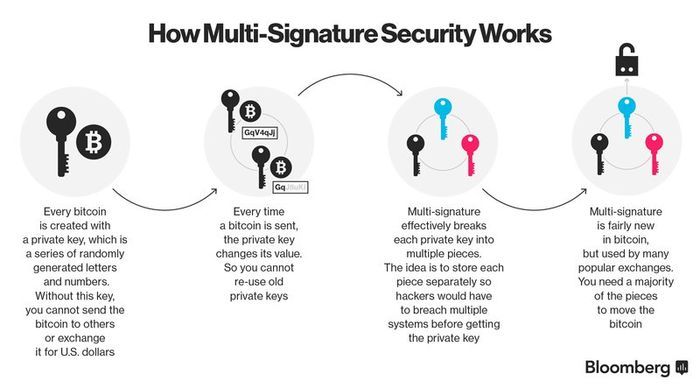
As the limitations of single-signature wallets became apparent, the cryptocurrency community turned to a concept borrowed from traditional banking: requiring multiple approvals for transactions. Multi-signature, or "multisig," wallets represent the first major evolution beyond the basic seed phrase model, introducing the principle of distributed control to cryptocurrency security.
To understand multisig wallets, imagine a business bank account that requires two signatures on every check. This dual-control system prevents any single person from embezzling funds while still allowing legitimate transactions to proceed smoothly. A multi signature wallet, often referred to as a multi-signature wallet, is a specialized type of cryptocurrency wallet designed to enhance transaction security by requiring multiple signatures before a transaction can be executed.
The technical implementation involves creating a special type of cryptocurrency address that is controlled by multiple private keys rather than just one. These are often referred to as M-of-N transactions. For instance, you might create a 2-of-3 multisig wallet where three people hold private keys, but only two signatures are required to authorize any transaction. This configuration provides both security and practical flexibility.
The security benefits are immediately apparent. When used properly, a multi-sig wallet aims to offer additional security by eliminating the single point of failure risk associated with having one private key. A hacker would need to compromise multiple separate keys, likely stored in different locations by different people, to steal funds. This represents a significant escalation in the difficulty and coordination required for theft.
Beyond security, multisig wallets enable new forms of financial organization that were previously impossible or extremely complicated. A startup can create a treasury wallet where major expenditures require approval from multiple co-founders. Organizations, on the other hand, can collaboratively manage their assets with multi-signature approvals for security and transparency. Families can set up shared accounts for major purchases or inheritance planning. Investment groups can ensure that no single member can make unauthorized trades.
The technology has proven its worth in practice. The Safe multisig wallet is a secure crypto wallet trusted by Vitalik Buterin (Ethereum cofounder) and other leading Web3 projects to secure over USD 100 billion in crypto assets. This level of institutional adoption demonstrates that multisig has moved beyond experimental technology to become a battle-tested solution for high-value cryptocurrency storage.
However, multisig wallets introduce their own set of challenges and limitations. The most obvious is coordination complexity. Every transaction requires multiple parties to be available and willing to sign. If you need 3-of-5 signatures and two of your co-signers are traveling without access to their keys, legitimate transactions can be blocked. This coordination overhead can make multisig wallets impractical for day-to-day use.
The technical implementation also varies significantly between different blockchains. It is difficult for multisig wallet providers to securely support new chains as the few cryptocurrency protocols that support multisig have distinct implementations from one another. Bitcoin's multisig implementation differs from Ethereum's, which differs from newer blockchains like Solana or Cardano. This fragmentation means that multisig solutions often work well on one blockchain but require completely different implementations for others.
There's also the question of key management distribution. While multisig eliminates the single point of failure, it multiplies the seed phrase management problem. Now instead of securing one seed phrase, you have multiple parties each responsible for securing their own keys. It is essential to distribute multi-sig private key access among distinct entities. A multi-sig setup where a single entity holds multiple private keys and stores them in a single location is essentially the same as a single-key wallet.
The user experience challenges extend beyond technical complexity to social and organizational dynamics. Who controls the keys? How do you handle disputes? What happens if one of the key holders becomes unavailable or unwilling to cooperate? What if relationships change or someone becomes malicious? These human factors can be more challenging to manage than the technical aspects.
Despite these limitations, multisig wallets have found their niche in scenarios where the benefits outweigh the complexity. If you're looking for the best crypto multisig wallets, Sparrow Wallet stands out for its comprehensive features and high level of security. Safe Wallet, formerly known as Gnosis Safe, is a popular multi-signature smart contract wallet. These established solutions demonstrate that multisig technology has matured and found practical applications.
The institutional adoption of multisig technology has been particularly significant. BitGo is a multi-sig wallet solution tailored for institutional investors and businesses. It supports a wide range of cryptocurrencies and offers enterprise-grade security features, including multi-user access and advanced policy controls. This corporate adoption has driven improvements in user interfaces, policy management, and integration with existing business processes.
Yet even as multisig wallets have gained acceptance, their limitations have pointed toward the need for more sophisticated solutions. The coordination overhead, blockchain-specific implementations, and social complexities of managing multiple keys have led researchers and developers to explore alternatives that could provide multisig's security benefits without its operational drawbacks.
The Cutting Edge: Multi-Party Computation Wallets
As the cryptocurrency ecosystem matured and institutional adoption accelerated, the limitations of both single-signature and multi-signature approaches became increasingly apparent. The industry needed a solution that could provide enterprise-grade security without the operational overhead of traditional multisig, while still maintaining the self-custody principles that make cryptocurrency valuable. The answer emerged from an advanced area of cryptography called multi-party computation, or MPC.
MPC enables multiple parties – each holding their own private data – to evaluate a computation without ever revealing any of the private data held by each party (or any otherwise related secret information). In the context of cryptocurrency wallets, this means that multiple parties can collaborate to sign transactions without any single party ever having access to the complete private key.
This represents a fundamental shift in how we think about key management. Traditional wallets store a complete private key somewhere, whether on a device, on paper, or in someone's memory. Even multisig wallets require complete private keys to be held by each party. MPC wallets, by contrast, split the private key into mathematical shares that are distributed among multiple parties, ensuring that no single party has access to the complete private key, eliminating single points of failure.
The technical elegance of MPC lies in its use of cryptographic protocols that allow computation on encrypted data. Think of it as a way for multiple people to jointly solve a mathematical equation without any of them knowing all the inputs. Each party holds a piece of the puzzle, and they can work together to create valid signatures without reconstructing the complete key. This process happens through sophisticated mathematical techniques involving threshold cryptography and distributed key generation.
The core mechanism that underpins MPC wallets is a sophisticated blend of distributed key generation (DKG) and threshold cryptography, two pillars of modern cryptography that enhance security and privacy in digital transactions. When you create an MPC wallet, the system generates key shares rather than a complete private key. These shares are mathematically related to each other in such a way that a predetermined threshold number of them can be combined to create valid signatures, but fewer than the threshold reveals no information about the key.
The security benefits are substantial. Unlike traditional wallets (EOAs), that solely rely on a single private key, MPC wallets meaning use advanced cryptographic technology, to ensure that the private key is neither exposed to nor stored in a single direction, adding an extra layer of security. An attacker would need to compromise multiple independent systems simultaneously to steal funds, and even then, the compromise would be mathematically complex rather than simply copying a file or seed phrase.
Perhaps more importantly, MPC wallets eliminate many of the usability problems that have plagued traditional approaches. Unlike multisig wallets, which require coordination among multiple parties for every transaction, MPC wallets can be configured so that a subset of key shares can authorize transactions. This means that legitimate users can transact smoothly while still maintaining security against compromise of any individual component.
The technology has rapidly gained adoption among institutional players who need to balance security with operational efficiency. Fireblocks has established itself as the gold standard for institutional MPC wallets. The platform is trusted by banks, hedge funds, and asset managers because of its multi-layered security, automated transaction workflows, and compliance-first approach. This institutional validation demonstrates that MPC has moved beyond academic research to become practical technology for managing large-scale cryptocurrency operations.
The blockchain compatibility advantages of MPC are particularly significant. The MPC system developed in-house at Coinbase supports both ECDSA and EdDSA protocols. This means the wallet can handle cryptographic signing for almost any blockchain, and users don't have to pay for gas transactions since there is zero overhead. Unlike multisig implementations, which must be built specifically for each blockchain's architecture, MPC signatures are indistinguishable from regular signatures at the blockchain level.
This universal compatibility is crucial as the cryptocurrency ecosystem becomes increasingly multi-chain. Unlike Multi-sig, MPC happens off-chain with only one single signature broadcast on-chain. It's data-light meaning it is cheaper and faster to execute, and much more secure. Users can manage assets across dozens of different blockchains using the same MPC wallet infrastructure, without needing to understand the specific multisig implementations of each chain.
The user experience improvements extend beyond technical compatibility to fundamental usability enhancements. Many MPC wallets are eliminating seed phrases entirely, instead using alternative recovery methods. Web3Auth: Wallet-as-a-service infrastructure that is friendly both to dedicated developers and end-users, Web3Auth uses MPC technology to bring improved security to users without the need for seed phrases. This represents a potential solution to one of cryptocurrency's most persistent user experience problems.
Recovery mechanisms in MPC wallets can be far more sophisticated than traditional approaches. Instead of relying on users to safely store seed phrases, MPC wallets can implement social recovery, biometric authentication, or institutional backup services. Phantom and Bitget Wallet are leading the way in smart recovery, experimenting with hybrid MPC and account abstraction to provide seamless and user-friendly recovery options. These approaches maintain the security properties of self-custody while dramatically reducing the risk of user error.
The governance capabilities of MPC wallets also represent a significant advancement over traditional approaches. Create as many custom rules and policies as you want for different situations. Setting up well defined rules ensures that not a single transaction can be executed without the approval of the appointed persons. Organizations can implement complex approval workflows, spending limits, time locks, and other sophisticated controls that would be difficult or impossible with traditional wallet architectures.
However, MPC wallets are not without their challenges and limitations. The computational overhead, while manageable for institutions, can impact performance compared to simpler alternatives. While offering increased security, MPC wallets might slow down processes and require more communication compared to simpler methods. The cryptographic protocols require coordination among multiple parties, which can introduce latency, particularly in high-frequency trading scenarios.
The complexity of MPC implementations also raises questions about auditability and trust. It's also worth noting that not all MPC wallets are open-source or interoperable, which could limit their usability and compatibility with other systems. Users must trust that the cryptographic implementations are correct and secure, which can be challenging to verify without deep mathematical expertise.
Despite these challenges, the trajectory of MPC wallet development suggests that they represent the future of cryptocurrency self-custody. In 2025, several MPC wallets stand out for their unique features and user benefits. Institutional platforms such as Ledger Vault, Fordefi, and Coinbase WaaS are leveraging MPC to secure billions in digital assets with multi-user access and hardware-grade protection.
Comparative Analysis: Security, Usability, and Control
Understanding the relative strengths and weaknesses of seed phrase, multisig, and MPC approaches requires examining them across multiple dimensions that matter to real users and organizations. Each technology represents different tradeoffs between security, usability, cost, and control, and the optimal choice depends heavily on the specific use case and user requirements.
From a pure security standpoint, the progression from seed phrases to multisig to MPC represents a clear evolution toward more sophisticated threat models. Seed phrases, while cryptographically sound, create a single point of failure that has proven vulnerable to both technical attacks and human error. The simplicity that makes seed phrases accessible also makes them fragile. A single moment of carelessness – a screenshot saved to the cloud, a handwritten phrase left visible, a moment of confusion during a phishing attack – can result in complete loss of funds.
Multisig wallets address this single point of failure by distributing control, but they do so in a way that increases surface area for certain types of attacks. While it becomes much harder for an attacker to compromise multiple independent keys, the coordination required for legitimate transactions creates new vulnerabilities. Social engineering attacks can become more sophisticated, targeting relationships between key holders rather than technical infrastructure. The human factors that make multisig appealing – the ability to involve trusted parties in financial decisions – also create new attack vectors that don't exist with individual custody.
MPC wallets represent a significant advancement in addressing both technical and human vulnerabilities. By ensuring that complete private keys never exist in any single location, they eliminate entire categories of attacks while maintaining usability. The mathematical properties of MPC mean that compromising individual key shares reveals no useful information to attackers, making the system resilient to partial breaches. However, the complexity of MPC implementations introduces new categories of potential vulnerabilities related to protocol implementation and coordination mechanisms.
The usability spectrum tells a different story. Seed phrases, despite their security limitations, offer unmatched simplicity for individual users who understand their responsibilities. There are no coordination requirements, no technical protocols to understand, and no dependencies on other parties or services. This simplicity has enabled the grassroots adoption of cryptocurrency and remains crucial for scenarios where complete individual sovereignty is paramount.
Multisig wallets sacrifice individual simplicity for organizational robustness. The coordination overhead that makes them less suitable for individual day-to-day use becomes an advantage in scenarios where deliberate friction is desirable. Corporate treasuries, DAO governance, and family inheritance planning all benefit from requiring multiple parties to agree on transactions. However, this coordination requirement can make multisig wallets impractical for scenarios requiring quick response to market movements or frequent transactions.
MPC wallets aspire to combine the security benefits of multisig with the usability of individual wallets, and in many respects they succeed. The ability to set flexible threshold requirements means that routine transactions can be frictionless while maintaining protection against compromise. Advanced features like programmable policies and automated compliance checking can actually make MPC wallets more usable than traditional alternatives for sophisticated use cases.
The cost considerations vary significantly across these technologies and use cases. Seed phrase management appears free but actually involves hidden costs in the form of security infrastructure, backup procedures, and risk management. Users who properly secure seed phrases often invest in safety deposit boxes, fireproof safes, or professional storage services. The psychological cost of constantly worrying about seed phrase security also represents a real burden for many users.
Multisig wallets have explicit coordination costs in terms of time and communication, but they can actually reduce total security costs by distributing responsibility. Instead of each individual bearing the full burden of perfect security practices, the risk is shared among multiple parties. However, the blockchain-specific nature of multisig implementations can create significant development and maintenance costs for organizations operating across multiple chains.
MPC wallets often have higher upfront costs due to their technical sophistication, but they can provide significant operational savings for organizations with complex security requirements. The ability to implement automated compliance checking, flexible approval policies, and universal blockchain compatibility can reduce ongoing administrative overhead. For institutional users, the reduced insurance and audit costs often justify the technology premium.
The control dimension reveals fundamental philosophical differences between these approaches. Seed phrases represent the purest form of individual sovereignty – complete control with complete responsibility. This aligns perfectly with cryptocurrency's original vision of eliminating trusted intermediaries, but it places enormous burdens on individual users. The "not your keys, not your crypto" principle reaches its logical conclusion with seed phrase management, but this absolute control comes at the cost of flexibility and error recovery.
Multisig wallets introduce structured interdependence while maintaining self-custody principles. Control is distributed by design, which can be either a feature or a limitation depending on the use case. For organizations, this structured sharing of control enables governance and risk management practices that would be impossible with individual keys. For individuals, it can provide security benefits while requiring trust in other parties.
MPC wallets offer perhaps the most nuanced approach to control. They can provide individual control that feels like traditional seed phrase management while actually distributing security responsibilities across multiple components. This hidden distribution can provide security benefits without requiring users to actively manage relationships with other parties. However, it also introduces dependencies on service providers and technical infrastructure that some users may find philosophically inconsistent with self-custody principles.
The accessibility implications of these technologies extend beyond individual users to broader cryptocurrency adoption. Seed phrases, despite their conceptual simplicity, have proven to be a significant barrier to mainstream adoption. We found that the majority of our participants harbored significant misconceptions about seed phrases that could expose them to significant security risks — e.g., only 43% could correctly identify an image of a seed phrase, many believed they could reset their seed phrase if they lost them.
Multisig wallets require even higher levels of technical and social sophistication, making them suitable primarily for organizations or technically savvy individuals. The coordination requirements alone eliminate many potential users, and the blockchain-specific implementations create additional barriers to entry.
MPC wallets show the most promise for bridging the gap between sophisticated security and mainstream accessibility. By abstracting away cryptographic complexity and eliminating seed phrase management, they could enable widespread self-custody adoption among users who would otherwise rely on centralized exchanges or custodial services.
Trust Models and Decentralization Philosophy
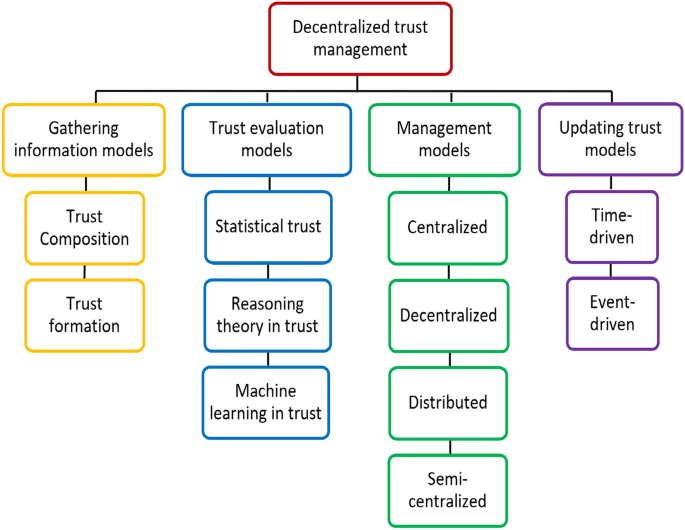
The evolution of wallet technologies reflects deeper questions about the nature of trust in decentralized systems. While all three approaches maintain the fundamental principle of self-custody – meaning users retain ultimate control over their assets – they implement dramatically different trust models that have profound implications for both security and philosophical consistency with cryptocurrency's founding principles.
Seed phrase wallets represent the most radical interpretation of trustlessness. In this model, trust is not distributed or managed – it is eliminated as much as possible. The user trusts only in mathematics and cryptography, not in any external parties, services, or coordination mechanisms. This aligns perfectly with the cypherpunk philosophy that inspired Bitcoin's creation, where the goal was to create a system that could function without requiring trust in governments, banks, or other traditional institutions.
The philosophical purity of this approach is compelling, but it places enormous practical burdens on users. When you eliminate external trust, you must internalize all responsibility. Every security decision, every backup procedure, and every access control mechanism becomes the individual's responsibility. The system cannot help you if you make mistakes because helping would require introducing trusted elements that could be compromised or corrupted.
This trust-elimination approach has proven both powerful and problematic. It has enabled cryptocurrency to function across political boundaries, survive regulatory attacks, and provide financial access to people excluded from traditional banking systems. However, it has also resulted in massive losses due to user error and has created barriers to adoption that limit cryptocurrency's potential social impact.
Multisig wallets introduce structured trust relationships while attempting to maintain decentralization principles. Rather than eliminating trust, they distribute it among multiple parties based on explicit agreements and technical controls. This represents a middle ground between individual sovereignty and collective security, but it also introduces social complexities that can be difficult to manage.
The trust model in multisig systems depends heavily on the relationships between key holders. In corporate settings, these relationships are typically defined by employment contracts, fiduciary duties, and legal frameworks. The trust is structured and legally enforceable, making it relatively predictable and manageable. In informal settings – such as family inheritance planning or community treasuries – the trust relationships are more personal and potentially more fragile.
The technical trust assumptions in multisig systems are generally well-understood and aligned with decentralization principles. The blockchain itself enforces the multisig requirements, and no external parties can override the mathematical rules that govern transaction authorization. However, the coordination mechanisms often rely on external communication channels and decision-making processes that can introduce trusted elements.
MPC wallets represent the most sophisticated approach to trust management, using cryptographic techniques to create trust relationships that are simultaneously distributed and invisible to users. This approach attempts to provide the security benefits of distributed trust without requiring users to actively manage social relationships or coordination mechanisms.
The technical trust model in MPC systems is complex and varies significantly between implementations. In threshold MPC systems, trust is distributed among multiple computational parties, but users must trust that these parties will remain available and honest. The two basic properties that a multi-party computation protocol must ensure are: Privacy: The private information held by the parties cannot be inferred from the execution of the protocol. Accuracy: If a number of parties within the group decide to share information or deviate from the instructions during the protocol execution, the MPC will not allow them to force the honest parties to output an incorrect result.
However, the practical trust requirements in MPC systems can vary dramatically depending on the implementation model. Self-hosted MPC systems, where users run their own MPC nodes, maintain strong decentralization properties but require significant technical expertise. Hosted MPC services, where third parties manage the computation infrastructure, provide better usability but introduce trust relationships with service providers that may not align with pure self-custody principles.
The philosophical implications of these different trust models extend beyond individual security considerations to questions about the future of financial sovereignty. Seed phrase systems embody the most radical vision of individual financial autonomy, but their practical limitations may limit their applicability to a relatively small group of technically sophisticated users.
Multisig systems suggest that financial sovereignty can be compatible with structured social relationships and organizational governance. This model may be more suitable for institutions and communities that want to maintain self-custody while implementing collective decision-making processes. The success of multisig systems in corporate and DAO contexts demonstrates that decentralization doesn't require eliminating all forms of structured trust.
MPC systems present the most complex philosophical questions because they can hide trust relationships behind cryptographic abstractions. On one hand, they offer the potential to provide strong security guarantees while maintaining excellent usability, potentially enabling mainstream adoption of self-custody principles. On the other hand, they may undermine the transparency and user control that many consider essential to cryptocurrency's value proposition.
The question of auditability becomes crucial in evaluating these trust models. Seed phrase systems are completely auditable by users – anyone can verify the mathematical relationship between their seed phrase and their private keys using open-source software. Multisig systems are partially auditable – users can verify the technical properties of their multisig arrangements but must rely on social trust for coordination mechanisms.
MPC systems present the greatest auditability challenges because the cryptographic protocols are complex and the distributed computation infrastructure may not be transparent to users. It's also worth noting that not all MPC wallets are open-source or interoperable, which could limit their usability and compatibility with other systems. This opacity doesn't necessarily indicate problems, but it does require users to trust mathematical proofs and implementation quality rather than being able to verify security properties directly.
The decentralization implications of these trust models also vary significantly. Seed phrase systems are maximally decentralized at the individual level but may contribute to centralization at the ecosystem level if their difficulty drives users toward custodial services. Multisig systems maintain decentralization by distributing control among multiple parties, but they require coordination mechanisms that may introduce centralized elements.
MPC systems can potentially provide strong decentralization properties while maintaining usability, but this depends heavily on the specific implementation model. Centralized MPC services may provide better user experience while undermining decentralization goals. Decentralized MPC networks may preserve philosophical consistency while introducing new technical and economic challenges.
Real-World Applications and Use Cases
The theoretical advantages and disadvantages of different wallet technologies become clearer when examined through the lens of real-world applications. Different organizations and individuals have found that their specific security requirements, operational constraints, and risk tolerance favor different approaches, creating a diverse ecosystem where multiple technologies coexist and serve different needs.
Individual retail users represent the largest potential market for wallet technologies, but their needs vary dramatically based on technical sophistication, asset values, and usage patterns. For users who make infrequent transactions and have developed strong security practices, seed phrase wallets remain an attractive option. The simplicity and complete control they provide align well with the philosophical motivations that draw many people to cryptocurrency in the first place.
However, seed phrase management has proven particularly challenging for users who are new to cryptocurrency or who lack strong technical backgrounds. We found that the majority of our participants harbored significant misconceptions about seed phrases that could expose them to significant security risks. This has created a significant barrier to mainstream adoption, as many potential users are deterred by the responsibility of managing seed phrases safely.
For these users, MPC wallets offer a promising alternative that maintains self-custody while reducing the burden of key management. The Zengo wallet is a crypto wallet solution that lets users create self-custody wallets that don't require seed phrases or keys. This approach eliminates one of the most significant user experience barriers while maintaining the security benefits of distributed key storage.
Corporate treasury management represents one of the most successful applications of multisig technology. Companies that hold significant cryptocurrency assets need to balance security against operational efficiency while meeting regulatory and audit requirements. BitGo is a multi-sig wallet solution tailored for institutional investors and businesses. It supports a wide range of cryptocurrencies and offers enterprise-grade security features, including multi-user access and advanced policy controls.
The corporate use case demonstrates how multisig technology can actually improve usability by providing structured authorization processes that meet compliance requirements. Rather than requiring individual employees to manage seed phrases for corporate assets, multisig systems allow companies to implement approval workflows that align with existing business processes while maintaining cryptographic security.
However, corporate adoption has also driven the evolution toward MPC systems, which provide many of the same benefits with better operational efficiency. Fireblocks has established itself as the gold standard for institutional MPC wallets. The platform is trusted by banks, hedge funds, and asset managers because of its multi-layered security, automated transaction workflows, and compliance-first approach. The ability to implement complex policies and automated compliance checking makes MPC systems particularly attractive for institutions with sophisticated operational requirements.
Cryptocurrency exchanges and custodial services represent another important use case where different wallet technologies serve different operational needs. Many exchanges use multisig systems for their hot wallets, where the coordination overhead is manageable because transactions are processed by automated systems rather than human operators. The distributed nature of multisig provides security benefits while the operational overhead can be absorbed by automated infrastructure.
For cold storage of large assets, many institutional custodians have moved toward MPC systems that provide better security properties while maintaining operational flexibility. Fireblocks is an institutional digital asset custodian that offers an MPC wallet with support for over 30 blockchain protocols and 1,100 tokens. The universal blockchain compatibility is particularly valuable for custodians who need to support diverse client portfolios without maintaining separate infrastructure for each blockchain.
Decentralized Autonomous Organizations (DAOs) represent an interesting test case for wallet technologies because they combine the decentralization philosophy of cryptocurrency with practical governance requirements. Many DAOs have adopted multisig systems for their treasuries, finding that the coordination requirements align well with their governance processes. The need to gather multiple signatures for treasury transactions creates natural checkpoints that prevent unauthorized spending while ensuring that legitimate governance decisions can be implemented.
However, some DAOs are experimenting with MPC systems that allow for more sophisticated governance models. The ability to implement programmable policies and automated compliance checking can enable more complex governance structures while reducing the coordination overhead that can slow DAO operations.
Family and inheritance planning represents one of the most challenging applications for wallet technologies because it requires balancing security, accessibility, and social dynamics. Traditional seed phrase approaches create significant challenges for inheritance because they require either sharing sensitive information before death or accepting the risk that assets will be lost if something unexpected happens.
Multisig systems offer some advantages for inheritance planning by allowing family members to be involved in security without requiring complete trust. 22% of participants shared seed phrases for recovery purposes, many participants acknowledged the importance of planning for account recovery but did not take corresponding actions. However, the coordination requirements can create practical challenges, particularly if family members are geographically distributed or lack technical sophistication.
MPC systems show promise for inheritance planning because they can implement sophisticated recovery mechanisms without requiring active coordination among family members. Social recovery systems, biometric authentication, and institutional backup services can provide multiple paths to asset recovery while maintaining security against unauthorized access.
Cross-border payments and remittances represent another important use case where wallet technology choices have practical implications. For individuals sending money across international borders, the simplicity and universality of seed phrase systems can be advantageous because they don't require coordination with other parties or dependence on service providers that might not be available in all jurisdictions.
However, the risk of loss during international travel or in politically unstable regions makes seed phrase management particularly challenging. MPC systems that provide recovery mechanisms and reduce dependence on physical storage may be more practical for users in these scenarios.
The gaming and NFT ecosystems have become important testing grounds for wallet technology because they combine high transaction volumes with diverse user bases that include many people new to cryptocurrency. Traditional seed phrase management has proven to be a significant barrier to adoption in gaming applications, where users expect smooth onboarding experiences similar to traditional apps.
MPC wallets integrated into gaming applications can provide self-custody benefits without requiring users to understand complex key management concepts. Additionally, embedded wallets from platforms like Coinbase, Binance, and Web3Auth are integrating MPC into their SDKs, enabling apps and games to offer secure, self-custodial wallets with social or biometric recovery options. This embedded approach may be crucial for bringing self-custody to mainstream consumer applications.
Technical Deep Dive: How These Systems Actually Work
Understanding the practical implementation of different wallet technologies requires examining the underlying cryptographic and computational mechanisms that enable their security properties. While users don't need to understand these technical details to use these systems effectively, the implementation differences have important implications for security, performance, and long-term viability.
Seed phrase systems rely on well-established cryptographic standards that have been refined over decades of development. The process begins with entropy generation, where the wallet software creates a random number with sufficient entropy to ensure cryptographic security. This entropy is then converted into a sequence of words using the BIP-39 standard, which defines a list of 2048 words and the mathematical relationship between entropy and word sequences.
The seed phrase serves as input to a key derivation function that generates the actual cryptographic keys used for transactions. The BIP-32 standard defines how to derive multiple keys from a single seed, enabling wallets to generate unlimited addresses for privacy and organizational purposes. The mathematical relationship between the seed phrase and derived keys is deterministic, meaning that the same seed phrase will always generate the same keys, enabling wallet recovery on different devices.
The security of seed phrase systems depends entirely on the randomness of the initial entropy generation and the secrecy of the resulting seed phrase. The cryptographic algorithms themselves are well-tested and considered secure against all known attacks, but the system provides no protection against compromise of the seed phrase itself. This creates the fundamental vulnerability that has driven development of alternative approaches.
Multisig systems extend the basic cryptographic model by requiring multiple signatures to authorize transactions. The technical implementation varies significantly between different blockchains, but the general principle involves creating special transaction types that specify multiple public keys and a threshold number of required signatures.
In Bitcoin's implementation, multisig transactions use script opcodes that define the signature requirements directly in the blockchain transaction. A 2-of-3 multisig transaction includes three public keys and requires two valid signatures from the corresponding private keys. The Bitcoin network validates these signatures using the same cryptographic algorithms used for single-signature transactions, but applies them to multiple key pairs.
Ethereum's approach to multisig is different because it relies on smart contracts rather than native blockchain features. Multisig wallets on Ethereum are implemented as smart contracts that store multiple public keys and implement logic to verify signatures before executing transactions. This approach provides more flexibility in terms of policy implementation but requires more computational resources and gas fees.
The security properties of multisig systems depend on the assumption that compromising multiple independent private keys is significantly more difficult than compromising a single key. This assumption generally holds in practice, but it requires that the keys be truly independent – stored in different locations, managed by different parties, and protected by different security measures.
MPC systems use more sophisticated cryptographic techniques that enable multiple parties to collectively sign transactions without any party having access to the complete private key. The technical implementation involves several advanced cryptographic concepts working together to provide the desired security properties.
Threshold secret sharing forms the foundation of most MPC implementations. This technique allows a secret (the private key) to be divided into multiple shares such that a predetermined threshold number of shares can reconstruct the secret, but fewer shares reveal no information about it. For example, in a 3-of-5 threshold scheme, any 3 shares can be combined to reconstruct the private key, but knowing only 2 shares provides no useful information to an attacker.
However, simply splitting a private key into shares and recombining them when needed would defeat the purpose of MPC, because it would require reconstructing the complete private key at some point. True MPC protocols use techniques like secure multiparty computation to perform cryptographic operations directly on the shared values without ever reconstructing the complete key.
The practical implementation of MPC signatures typically involves a multi-round protocol where the parties holding key shares exchange specially crafted messages that allow them to collectively generate a valid signature. The exact protocol varies depending on the signature algorithm and security requirements, but the general principle is that each party performs local computations on their key share and shares intermediate results that can be combined to produce the final signature.
The two basic properties that a multi-party computation protocol must ensure are: Privacy: The private information held by the parties cannot be inferred from the execution of the protocol. Accuracy: If a number of parties within the group decide to share information or deviate from the instructions during the protocol execution, the MPC will not allow them to force the honest parties to output an incorrect result.
The distributed key generation process in MPC systems is particularly sophisticated because it must create key shares without ever creating the complete private key. This involves cryptographic protocols where multiple parties contribute randomness and perform joint computations to generate key shares that are mathematically related but individually reveal no information about the final key.
The performance implications of these different approaches vary significantly. Seed phrase systems have minimal computational overhead because they use standard cryptographic operations that are highly optimized in most software and hardware implementations. The only performance consideration is the key derivation process, which is intentionally designed to be computationally expensive to slow down brute force attacks, but this only affects wallet creation and recovery, not routine transactions.
Multisig systems have moderate performance overhead compared to single-signature transactions because they require multiple signature verifications. In Bitcoin, this primarily affects transaction size and validation time. In Ethereum, multisig transactions can require significantly more gas because they involve smart contract execution rather than simple signature verification.
MPC systems have the highest computational overhead because they require multiple rounds of communication and cryptographic computation to generate each signature. While offering increased security, MPC wallets might slow down processes and require more communication compared to simpler methods. However, this overhead is generally acceptable for most applications, and ongoing research is focused on optimizing MPC protocols to reduce latency and computational requirements.
The network communication requirements also differ significantly between these approaches. Seed phrase systems require no coordination, making them ideal for offline or air-gapped environments. Multisig systems require coordination among key holders but only at the time of transaction authorization. MPC systems require more extensive communication between parties during the signature generation process, which can create challenges in high-latency or unreliable network environments.
The blockchain compatibility implications are particularly important as the cryptocurrency ecosystem becomes increasingly multi-chain. Seed phrase systems work universally because they generate standard private keys that are compatible with any blockchain using the same cryptographic algorithms. Multisig systems require blockchain-specific implementations because each blockchain handles multisig transactions differently.
Unlike Multi-sig, MPC happens off-chain with only one single signature broadcast on-chain. It's data-light meaning it is cheaper and faster to execute, and much more secure. This blockchain-agnostic property makes MPC systems particularly attractive for organizations that need to operate across multiple blockchain ecosystems without maintaining separate infrastructure for each.
Economic Implications and Market Impact
The evolution of wallet technologies is reshaping the economic landscape of cryptocurrency in ways that extend far beyond individual user security. The different approaches to key management create distinct cost structures, risk profiles, and market dynamics that influence everything from institutional adoption to the development of new financial products and services.
The direct costs associated with different wallet technologies vary significantly and often include hidden expenses that become apparent only through long-term use. Seed phrase management appears to have minimal direct costs, but proper security requires investments in storage infrastructure that many users underestimate. Professional-grade storage solutions such as bank safety deposit boxes, fireproof safes, or specialized storage services can cost hundreds or thousands of dollars annually for users with significant assets.
The insurance implications are particularly important for institutional users. Traditional insurance policies generally don't cover cryptocurrency losses, and specialized cryptocurrency insurance is expensive and often requires specific security measures. Seed phrase systems typically receive the lowest insurance coverage because of the single point of failure risk, while multisig and MPC systems can qualify for better coverage terms due to their distributed security models.
In 2023 alone, approximately $3.8 billion worth of cryptocurrency was stolen through various cyberattacks, with a significant portion attributed to single-signature wallet vulnerabilities. Multisig wallets have proven to be an effective deterrent, reducing the risk of unauthorized access by over 60%. These statistics translate directly into insurance pricing and risk assessment, making advanced wallet technologies increasingly attractive from a total cost of ownership perspective.
The operational costs associated with different wallet technologies create different economic incentives for various types of organizations. Small individual users may find seed phrase management to be the most cost-effective approach despite the risks, while larger organizations often discover that the coordination and security costs of multisig systems are justified by the risk reduction they provide.
MPC systems typically have higher upfront costs due to their technical complexity, but they can provide significant operational savings for organizations with complex security requirements. What sets Fireblocks apart is its network of 1,800+ institutions, allowing instant, secure settlements without counterparty risk. This network effect creates economies of scale that can make MPC systems more cost-effective than traditional approaches for institutions that frequently transact with other network participants.
The impact on transaction costs varies significantly between blockchain networks and transaction types. Bitcoin multisig transactions are larger than single-signature transactions, resulting in higher transaction fees during periods of network congestion. Ethereum multisig transactions require more gas because they involve smart contract execution, making them significantly more expensive than simple transfers.
A key feature of TotalSig is its ability to optimize transaction fees, potentially reducing them by 3 to 5 times. This is especially valuable during periods of high gas prices, allowing users to save significant amounts per transaction and providing cost-effective solutions during network congestion. This demonstrates how advanced wallet technologies can actually reduce transaction costs through optimization techniques that aren't available with simpler approaches.
The market impact of wallet technology evolution extends to the development of new financial products and services. The security limitations of seed phrase systems have created a large market for custodial services, where institutions manage cryptocurrency on behalf of users who don't want to handle key management themselves. This custodial market represents billions of dollars in assets under management and generates significant fee revenue for service providers.
However, the emergence of more user-friendly self-custody solutions could potentially disrupt this market. If MPC wallets and other advanced technologies can provide institutional-grade security with consumer-friendly usability, they might enable users to maintain self-custody without sacrificing convenience. This could reduce demand for custodial services and shift value to wallet infrastructure providers.
The institutional adoption patterns reveal important economic dynamics in the wallet technology market. Early institutional adopters often chose multisig solutions because they were the most mature alternative to single-signature wallets. However, many institutions are now migrating to MPC systems as they mature and offer better operational efficiency.
Looking ahead to the second half of 2025, several developments are expected. Bitcoin.com Wallet will integrate deeper Zano support for private payments and improve smart recovery features. Binance Web3 Wallet will add gasless transaction support and biometric recovery tools. MetaMask Institutional will expand its MPC custodian integrations, offering more control and compliance-ready infrastructure. This institutional migration toward MPC systems reflects their economic advantages for complex organizational use cases.
The competitive dynamics in the wallet technology market are being shaped by the different value propositions of these technologies. Seed phrase wallets compete primarily on simplicity and cost, making them attractive for individual users and small organizations with limited security budgets. Multisig solutions compete on proven security and regulatory compliance, appealing to institutions that need established solutions with clear audit trails.
MPC systems compete on the promise of combining the security benefits of multisig with the usability of single-signature systems, but they must overcome higher costs and technical complexity to achieve market adoption. The success of MPC providers will likely depend on their ability to deliver on this value proposition while building ecosystem partnerships that justify the technology premium.
The network effects associated with different wallet technologies create interesting economic dynamics. Seed phrase systems benefit from universal compatibility and the large ecosystem of supporting tools and services. Multisig systems benefit from institutional adoption and regulatory acceptance, creating credibility that drives further adoption.
MPC systems are attempting to create network effects through platform strategies, where multiple services build on common MPC infrastructure. The public crypto exchange's MPC wallet enables a large and growing number of users to access the Web3 ecosystem in a safe, reliable, and secure manner. If successful, these platform strategies could create powerful economic moats that favor early MPC adopters.
The impact on cryptocurrency adoption more broadly may be the most significant economic implication of wallet technology evolution. The complexity and risk associated with seed phrase management has been identified as a major barrier to mainstream cryptocurrency adoption. If advanced wallet technologies can reduce this barrier while maintaining the self-custody benefits that make cryptocurrency valuable, they could unlock much larger markets.
However, the economic incentives around wallet technology development create potential conflicts with decentralization principles. Companies that invest in developing advanced wallet technologies need to generate returns on their investments, which may lead them toward business models that concentrate control or extract value in ways that contradict cryptocurrency's philosophical foundations.
The regulatory implications of different wallet technologies also have significant economic consequences. Regulators are generally more comfortable with multisig systems because they provide clear audit trails and can implement compliance controls that are difficult or impossible with individual seed phrase management. MPC systems may offer even better compliance capabilities while maintaining user control, potentially reducing regulatory friction for cryptocurrency businesses.
Challenges and Limitations
Despite the technological advances represented by multisig and MPC wallets, each approach faces significant challenges that limit their applicability and effectiveness in certain scenarios. Understanding these limitations is crucial for making informed decisions about wallet technology adoption and for identifying areas where further innovation is needed.
User education remains a fundamental challenge across all wallet technologies, but the nature of the educational burden varies significantly. While seed phrase management appears conceptually simple, many believed they could reset their seed phrase if they lost them, indicating that even basic concepts are widely misunderstood. This educational gap contributes to security vulnerabilities and user losses that undermine confidence in self-custody approaches.
Multisig systems introduce different educational challenges because users must understand not only the technical aspects of key management but also the social dynamics of coordination and governance. The technical knowledge required to set up and maintain multisig wallets is often beyond the capabilities of individual users, limiting adoption to organizations with dedicated technical resources.
MPC systems present perhaps the greatest educational challenge because they abstract away the underlying security mechanisms in ways that can be difficult for users to verify or understand. While this abstraction can improve usability, it can also create false confidence or inappropriate trust in systems that users cannot fully evaluate. The complexity of the underlying cryptography makes it difficult for users to distinguish between well-implemented and poorly-implemented MPC systems.
The standardization challenges facing the wallet technology ecosystem create fragmentation that limits interoperability and increases development costs. While seed phrase systems benefit from well-established standards like BIP-39 and BIP-32, multisig implementations vary significantly between different blockchains and wallet providers. It is difficult for multisig wallet providers to securely support new chains as the few cryptocurrency protocols that support multisig have distinct implementations from one another.
MPC systems face even greater standardization challenges because the technology is newer and the implementation space is more complex. Different MPC protocols offer different tradeoffs between security, performance, and functionality, making it difficult to establish universal standards. The lack of standardization creates vendor lock-in risks and makes it difficult for users to migrate between different MPC providers.
Recovery and inheritance planning present persistent challenges across all wallet technologies, but the specific obstacles vary significantly. Seed phrase systems require users to securely share sensitive information with trusted parties or accept the risk of permanent loss. The social dynamics of sharing seed phrases often conflict with security best practices, creating difficult tradeoffs between accessibility and protection.
Moreover, only a minority have engaged in any estate planning for their crypto assets. This lack of planning creates significant risks for asset recovery and inheritance, particularly given the irreversible nature of cryptocurrency transactions. Traditional legal frameworks for inheritance often don't accommodate the unique properties of cryptographic assets, creating additional complexity for families and estates.
Multisig systems can provide better inheritance planning capabilities by allowing multiple parties to be involved without sharing complete control, but they introduce coordination challenges that can be difficult to manage across generations or changing family relationships. The technical requirements for maintaining multisig wallets over long periods can create dependencies on specific service providers or technical expertise that may not be sustainable.
MPC systems offer promise for addressing inheritance challenges through sophisticated recovery mechanisms, but they often require trust in service providers or infrastructure that may not be available indefinitely. The long-term viability of MPC services is difficult to evaluate, creating risks for users who depend on them for asset recovery.
Performance and scalability limitations affect different wallet technologies in different ways. Seed phrase systems have minimal performance overhead for individual use, but they don't scale well to organizational use cases that require coordination among multiple parties. The lack of built-in authorization controls makes seed phrase systems unsuitable for complex governance requirements.
Multisig systems can handle complex authorization requirements effectively, but the coordination overhead limits their scalability for high-frequency transactions. The blockchain-specific nature of multisig implementations also creates scalability challenges for organizations operating across multiple networks.
The process of transaction authorization in MPC wallets, which requires collaboration among multiple parties, can introduce delays, especially in high-frequency trading environments. While MPC systems offer better scalability than traditional multisig for many use cases, the computational overhead and communication requirements can create bottlenecks in scenarios requiring rapid transaction processing.
Regulatory uncertainty creates challenges for all advanced wallet technologies, but the specific risks vary. Multisig systems are generally well-understood by regulators because they provide clear audit trails and can implement compliance controls. However, the distributed nature of key management can create challenges for meeting certain regulatory requirements, particularly in jurisdictions with strict custody regulations.
MPC systems present more complex regulatory challenges because the distributed nature of key management may not fit cleanly into existing regulatory frameworks. Regulators may struggle to understand which parties have custody and control over assets in MPC systems, potentially creating compliance challenges for institutional adopters.
The technical debt and maintenance challenges associated with different wallet technologies create long-term sustainability concerns. Seed phrase systems benefit from their simplicity and the maturity of supporting infrastructure, making them relatively easy to maintain over long periods. However, the security challenges associated with individual key management may become more severe as attack techniques evolve.
Multisig systems require ongoing maintenance to stay current with blockchain protocol changes and security best practices. The blockchain-specific nature of multisig implementations creates technical debt that can be expensive to maintain as the ecosystem evolves.
MPC systems face the greatest maintenance challenges due to their complexity and the rapid evolution of the underlying technology. The cryptographic protocols that underpin MPC systems continue to evolve, potentially requiring significant updates or migrations to maintain security and performance. The dependency on specialized expertise for maintenance makes MPC systems particularly vulnerable to technical debt accumulation.
Interoperability challenges limit the effectiveness of all wallet technologies in the increasingly multi-chain cryptocurrency ecosystem. While seed phrase systems provide good compatibility across different blockchains, they don't offer built-in solutions for cross-chain transactions or unified management of multi-chain portfolios.
Integrating MPC wallets seamlessly with the existing infrastructure of blockchain and cryptocurrency ecosystems can be difficult. This lack of interoperability might limit their widespread adoption as users and services look for solutions that can easily work within the current landscape.
The cost and accessibility barriers associated with advanced wallet technologies create challenges for widespread adoption. While the total cost of ownership may favor advanced systems for institutional users, the upfront costs and technical complexity can be prohibitive for individual users and small organizations. This creates a potential bifurcation in the market where advanced security is available primarily to well-resourced users.
Future Developments and Emerging Trends
The trajectory of wallet technology development suggests that we are approaching a period of rapid innovation and convergence, where the distinct categories of seed phrase, multisig, and MPC wallets may begin to blur as new hybrid approaches emerge. Several technological and market trends are shaping this evolution in ways that could fundamentally transform how people interact with cryptocurrency.
The integration of artificial intelligence and machine learning into wallet security represents one of the most promising areas of development. AI systems can potentially provide intelligent risk assessment, automated policy enforcement, and predictive security monitoring that could make all types of wallets more secure and user-friendly. Machine learning algorithms could analyze transaction patterns to detect suspicious activity, optimize fee structures, and even provide personalized security recommendations based on individual usage patterns.
Biometric authentication is becoming increasingly sophisticated and accessible, creating opportunities to replace or supplement traditional authentication methods across all wallet types. Advanced biometric systems could provide the security benefits of hardware tokens while offering the convenience of always-available authentication. The combination of biometric authentication with MPC systems could enable truly seamless self-custody experiences that don't require users to manage any traditional credentials.
Phantom will roll out smarter token and NFT data tools and test MPC-based recovery. Coinbase Wallet will continue embedding MPC-backed wallets into third-party apps through its WaaS SDK. This integration of MPC technology into consumer applications represents a significant trend toward making advanced security invisible to end users while maintaining the benefits of self-custody.
The development of account abstraction on Ethereum and other smart contract platforms is creating new possibilities for wallet functionality that blur the lines between traditional categories. Account abstraction (AA) is a blockchain feature that allows smart contracts to function as fully customizable wallets, removing the need for externally owned accounts (EOAs) like traditional Ethereum wallets. This capability enables wallets to implement complex authorization logic, automated transactions, and recovery mechanisms that were previously impossible.
Account abstraction could enable hybrid systems that combine elements of multisig and MPC technology while adding programmable features like automated compliance checking, conditional transactions, and social recovery mechanisms. These capabilities could make sophisticated wallet security accessible to mainstream users without requiring them to understand the underlying complexity.
The emergence of decentralized identity systems could provide new foundations for wallet security and recovery that don't depend on traditional seed phrases or centralized service providers. Decentralized identity could enable reputation-based recovery mechanisms, social attestation systems, and cross-platform identity verification that could make wallet management both more secure and more user-friendly.
Cross-chain interoperability continues to evolve rapidly, with new protocols and standards emerging to enable seamless asset management across multiple blockchain networks. The wallet technologies that can most effectively integrate with these interoperability solutions will likely have significant advantages in the increasingly multi-chain cryptocurrency ecosystem.
The revamped wallet is also gearing up to support all blockchains compatible with the Ethereum Virtual Machine (EVM) and select others, such as Solana. This trend toward universal blockchain support will likely favor MPC systems and account abstraction approaches that can provide consistent interfaces across different blockchain architectures.
The regulatory landscape is evolving in ways that could significantly impact wallet technology development. As governments around the world develop more sophisticated cryptocurrency regulations, wallet providers will need to implement compliance features that can satisfy regulatory requirements without compromising the benefits of self-custody.
The development of central bank digital currencies (CBDCs) could create new requirements for wallet interoperability and compliance monitoring that influence the design of all wallet technologies. While CBDCs may operate on different technical principles than existing cryptocurrencies, the wallet infrastructure that supports them will likely need to integrate with existing cryptocurrency systems.
Privacy-preserving technologies continue to advance, with new cryptographic techniques enabling stronger privacy protection without sacrificing security or compliance capabilities. Zero-knowledge proofs, homomorphic encryption, and other advanced cryptographic techniques could enable wallet systems that provide complete transaction privacy while still supporting regulatory compliance and audit requirements.
The integration of Internet of Things (IoT) devices and edge computing capabilities could enable new forms of distributed wallet security that take advantage of multiple connected devices. Rather than relying on centralized servers or coordination between human parties, future wallet systems could leverage the computational resources of multiple devices to provide distributed security while maintaining usability.
Quantum computing represents both a threat and an opportunity for wallet technology development. While quantum computers could potentially break existing cryptographic algorithms, they could also enable new forms of cryptographic security that are fundamentally more secure than current approaches. Wallet technologies that can adapt to post-quantum cryptography will have significant advantages as quantum computing capabilities advance.
The development of more sophisticated hardware security modules (HSMs) and trusted execution environments (TEEs) could enable new forms of secure computation that combine the benefits of hardware security with the flexibility of software-based systems. These technologies could enable MPC systems that provide better security guarantees while reducing the coordination overhead associated with current implementations.
Social recovery mechanisms are becoming more sophisticated and may represent a convergence point between different wallet approaches. Bitget Wallet will introduce a new "smart recovery" feature combining MPC and social login. These systems could provide the security benefits of distributed control while eliminating the coordination challenges that have limited multisig adoption.
The gamification of wallet security could make good security practices more engaging and accessible to mainstream users. By incorporating elements of gaming, achievement systems, and social interaction, wallet providers could encourage users to adopt better security practices while making the overall experience more enjoyable.
Automated compliance and reporting capabilities are becoming more sophisticated, potentially enabling wallet systems that can satisfy complex regulatory requirements without requiring manual intervention from users. These systems could automatically generate audit trails, enforce spending policies, and report transactions to relevant authorities while maintaining user privacy and control.
Recommendations and Best Practices
Navigating the complex landscape of wallet technologies requires a strategic approach that considers individual needs, risk tolerance, and technical capabilities. The decision between seed phrase, multisig, and MPC approaches should be based on careful evaluation of specific use cases rather than assuming that any single technology is universally optimal.
For individual users who are new to cryptocurrency or have limited technical expertise, the primary considerations should focus on balancing security with usability while minimizing the risk of permanent loss due to user error. Traditional seed phrase management may be appropriate for users who can commit to developing strong security practices and who value maximum control over their assets. However, this approach requires significant ongoing attention to security details and backup procedures.
As soon as you create a new wallet or key, make sure to record your recovery phrase with your preferred method. Self-custody wallet providers, including BitPay, do not save or take responsibility for your seed phrase. Users who choose seed phrase systems must immediately implement proper backup procedures and should never delay this critical security step.
For individual users who prioritize convenience or who are concerned about their ability to manage seed phrases safely, MPC wallets offer an increasingly attractive alternative. Zengo: With an excellent record as a safe self-custodial MPC wallet, Zengo makes asset management easier while providing stronger protection against unauthorized access. These systems can provide institutional-grade security while eliminating many of the user experience challenges associated with traditional key management.
However, users considering MPC systems should carefully evaluate the long-term viability and trustworthiness of the service providers they depend on. The distributed nature of MPC security provides protection against many types of attacks, but users must still trust that the service infrastructure will remain available and secure over time.
For organizations and institutions, the choice between multisig and MPC systems often depends on specific operational requirements and regulatory constraints. Organizations with established governance processes and clear authorization hierarchies may find that multisig systems align well with their existing procedures while providing clear audit trails and regulatory compliance.
The Safe multisig wallet is a secure crypto wallet trusted by Vitalik Buterin (Ethereum cofounder) and other leading Web3 projects to secure over USD 100 billion in crypto assets. This level of institutional adoption demonstrates that multisig technology has proven itself in high-stakes environments and can provide the security and governance capabilities that organizations require.
However, organizations that need to operate across multiple blockchain networks or that require high transaction throughput may find that MPC systems provide better operational efficiency. Fireblocks' institutional MPC wallet maximizes security and service level agreements (SLAs) while minimizing operational overhead. The universal blockchain compatibility and automated policy enforcement capabilities of advanced MPC systems can provide significant operational advantages for complex organizational use cases.
Estate planning and inheritance considerations should be a priority for all cryptocurrency users, regardless of which wallet technology they choose. Moreover, only a minority have engaged in any estate planning for their crypto assets. This lack of planning creates significant risks not only for individual users but also for the broader adoption of cryptocurrency as a store of value.
Users of seed phrase systems should implement comprehensive estate planning that includes secure storage of seed phrases in locations accessible to trusted family members or legal representatives. This often requires balancing the security risks of sharing sensitive information against the risks of assets becoming permanently inaccessible.
Multisig systems can provide better inheritance planning capabilities by allowing family members or legal representatives to be included as key holders without requiring them to have complete access to assets during the account holder's lifetime. However, this approach requires careful planning to ensure that the necessary technical knowledge and coordination capabilities will be available when needed.
MPC systems may offer the most flexible inheritance planning options through sophisticated recovery mechanisms that can be configured to provide access to designated parties under specific circumstances. However, users should ensure that these recovery mechanisms are properly documented and that designated beneficiaries understand how to use them.
Security practices should be adapted to the specific characteristics of each wallet technology while maintaining fundamental principles of defense in depth. For seed phrase systems, this means implementing multiple backup methods, using dedicated hardware for key generation and storage, and regularly testing recovery procedures to ensure they work correctly.
Use an offline backup method that can't be hacked, like copied on a piece of paper or engraved onto steel; store either at a secret location within a fire-proof personal safe or safety deposit box. Physical security measures remain crucial even for the most advanced wallet technologies, and users should implement multiple layers of protection against both digital and physical threats.
For multisig systems, security practices should focus on ensuring the independence of key holders and the security of coordination mechanisms. Key holders should use different devices, different storage methods, and different communication channels to minimize the risk of correlated failures. Regular testing of transaction authorization procedures can help identify potential coordination problems before they affect critical operations.
MPC systems require users to understand the trust assumptions associated with the specific implementation they choose. While the cryptographic protocols provide strong security guarantees, users must trust the service providers, software implementations, and communication infrastructure that enable the MPC functionality. Regular security audits and ongoing monitoring of service provider security practices are essential for maintaining confidence in MPC systems.
Risk management strategies should be tailored to the specific threats that are most relevant to each user's situation and wallet technology choice. Individual users in stable political and economic environments may focus primarily on protecting against theft, loss, and user error. Users in less stable environments may need to prioritize portability, censorship resistance, and protection against physical threats.
Institutional users typically face more complex risk management requirements that may include regulatory compliance, fiduciary responsibilities, and protection against insider threats. The wallet technology choices should align with the organization's broader risk management framework and should be regularly reviewed as business requirements and threat landscapes evolve.
Diversification across multiple wallet technologies can provide additional security benefits while reducing dependence on any single approach. Users with significant cryptocurrency holdings might consider distributing their assets across different wallet types to reduce the impact of any single point of failure. This approach requires additional complexity and coordination, but it can provide significant risk reduction benefits.
However, diversification should be implemented carefully to avoid creating new vulnerabilities through increased complexity. Each additional wallet system introduces new attack vectors and management overhead that must be carefully evaluated against the security benefits provided.
Final thoughts
The evolution of cryptocurrency wallet technologies from simple seed phrases to sophisticated multi-party computation systems represents more than just incremental security improvements. It reflects a fundamental maturation of the cryptocurrency ecosystem as it grapples with the challenge of making self-custody both secure and accessible to mainstream users. Each technological approach embodies different philosophical perspectives on the balance between individual sovereignty, collective security, and practical usability.
Seed phrases will likely remain relevant for users who prioritize maximum individual control and who have the knowledge and commitment required to manage them safely. Their simplicity and universal compatibility ensure that they will continue to serve as the foundation for cryptocurrency self-custody, even as more sophisticated alternatives become available. However, their limitations in terms of user experience and error tolerance suggest that they will increasingly become a niche solution rather than the default choice for most users.
Multisig wallets have found their niche in organizational and institutional contexts where the coordination overhead is justified by the security benefits and governance capabilities they provide. The proven track record of multisig technology in securing large-scale cryptocurrency assets demonstrates its value for specific use cases, even as its limitations prevent it from becoming a universal solution.
The rapid development and adoption of MPC wallet technology suggests that it may represent the future of mainstream cryptocurrency self-custody. By providing institutional-grade security with consumer-friendly usability, MPC systems could enable the widespread adoption of self-custody principles without requiring users to become cryptographic experts. However, the success of this approach depends on the development of sustainable business models, robust technical standards, and long-term trust relationships between users and service providers.
In conclusion, 2025 marks a significant shift towards MPC wallets, which offer enhanced security and user experience. Whether for individuals or institutions, MPC wallets provide a smart, adaptive gateway to self-sovereign finance, making crypto management safer and simpler. This technological shift could be the key that unlocks mainstream cryptocurrency adoption by eliminating the security and usability barriers that have limited adoption to date.
The convergence of wallet technologies with other emerging innovations such as account abstraction, decentralized identity, and cross-chain interoperability suggests that the future of cryptocurrency self-custody will be characterized by hybrid systems that combine elements from multiple approaches. Rather than competing technologies, we may see seed phrases, multisig, and MPC systems evolving into complementary components of more comprehensive security frameworks.
The implications of this technological evolution extend beyond individual user security to fundamental questions about the future of money and financial sovereignty. As wallet technologies become more sophisticated and user-friendly, they enable new forms of financial organization and governance that were previously impossible. The ability to implement programmable compliance, automated governance, and sophisticated risk management through wallet technology could transform not just how individuals manage their money, but how organizations, communities, and even governments organize their financial systems.
However, this technological progress also introduces new risks and challenges that must be carefully managed. The complexity of advanced wallet systems can create new forms of vendor dependence and systemic risk that could undermine the decentralization principles that make cryptocurrency valuable. The need to balance innovation with philosophical consistency will be an ongoing challenge for the cryptocurrency community.
The path forward requires continued investment in user education, technical standards development, and regulatory clarity to ensure that advanced wallet technologies can realize their potential while maintaining the principles of financial sovereignty and decentralization that define cryptocurrency's value proposition. The choices made by wallet developers, users, and regulators over the next few years will likely determine whether cryptocurrency achieves its promise of democratizing financial access or remains a niche technology for specialists.
Ultimately, the success of any wallet technology will be measured not just by its technical capabilities, but by its ability to empower individuals and organizations to take control of their financial lives while operating safely and effectively in an increasingly complex digital economy. The wallet technologies that can best serve this fundamental purpose while adapting to changing user needs and technological capabilities will shape the future of cryptocurrency and digital finance more broadly.
As we stand at this technological crossroads, the decisions made by individual users, organizations, and service providers will collectively determine which path the cryptocurrency ecosystem follows. The technologies exist to make self-custody both secure and accessible; the challenge now is implementing them in ways that honor cryptocurrency's founding principles while meeting the practical needs of a global financial system. The future of money may well depend on getting this balance right.